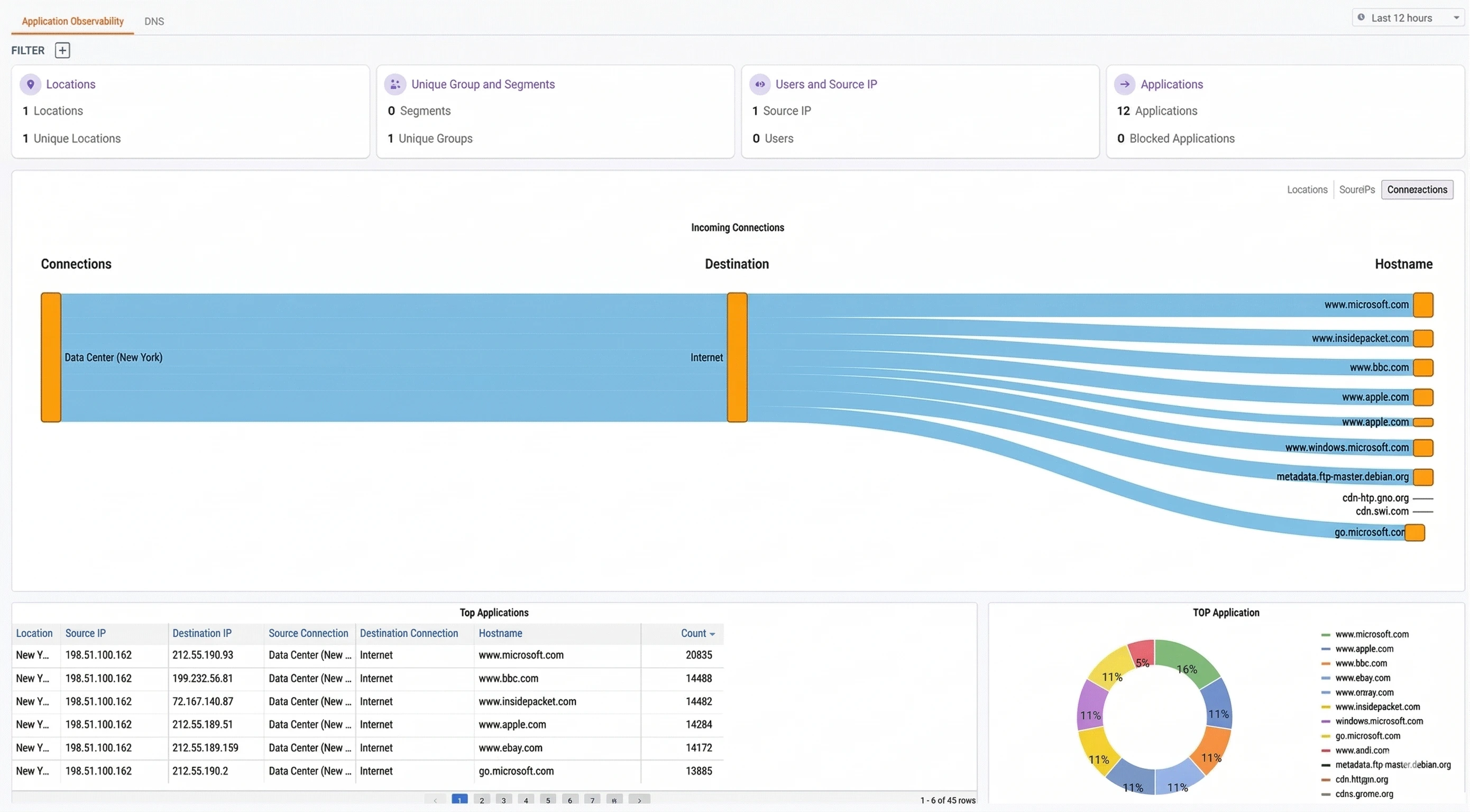
Date filter
In the upper right, use the date range selector to adjust the time window for all dashboard data (e.g., Last 12 hours, Last 24 hours, Last 7 days).Traffic filters
Below the tab name, the Filter option lets you narrow the dashboard data by criteria such as locations, IPs, and connections.Summary cards
At the top of the dashboard, four summary cards provide a quick snapshot of activity within the selected time window:| Card | Description |
|---|---|
| Locations | The number of physical locations generating application traffic |
| Unique Group and Segments | The number of network segments and unique groups observed in the traffic |
| Users and Source IP | The number of distinct source IP addresses and mapped users |
| Applications | The total number of applications detected, along with how many are currently blocked |
Incoming Connections
The center of the dashboard displays an Incoming Connections flow diagram. This is a Sankey-style visualization that maps the path of traffic from its source through to the destination hostnames.- Connections — The named connections originating the traffic (e.g., DIA_pool_1_NY)
- Destination — The destination category (e.g., Internet)
- Hostname — The specific hostnames receiving traffic, sized proportionally to their traffic volume
| Sub-tab | Description |
|---|---|
| Locations | Groups incoming connections by physical location |
| Source IPs | Groups incoming connections by source IP address |
| Connections | Groups incoming connections by named connection |
Top Applications
The bottom of the dashboard is divided into two sections:Top Applications table
A sortable table listing individual application flows with the following columns:| Column | Description |
|---|---|
| Location | The physical location where the traffic originated |
| Source IP | The source IP address initiating the connection |
| Destination IP | The destination IP address |
| Source Connection | The named source connection (e.g., DIA_pool_1_NY) |
| Destination Connection | The destination connection category (e.g., Internet) |
| Hostname | The resolved hostname of the destination |
| Count | The number of connections observed for this flow |